- January 20, 2023
- Posted by: Manoj Pandey
- Categories: Device Engineering, Digital Engineering

As the world becomes more connected with the Internet, cyber-security threats continue to increase. By understanding and managing assets, organisations can ensure their data and operations are secure from malicious attacks.
- How are today’s Industrial Organizations Stacking up in Cybersecurity?
- Bottlenecks that are Preventing in Advancement of Industrial Cybersecurity
- What are the Main Challenges when Securing IoT Devices?
- Importance of Building Cybersecurity into IoT Devices
- Cost of Staying still for Industries that Needs Cybersecurity
- How do Industrial Asset Manufacturers Make Sure of Industrial Cyber Security?
- How Kemsys can Help?
- Conclusion
Industrial asset management is crucial for the safe and efficient operation of industrial control systems (ICS) and other operational technology (OT) used in manufacturing, energy, and other critical infrastructure industries.
These systems control and monitor physical processes, such as the production of goods, the distribution of power, and the provision of water and other essential services. However, with the increasing use of digital technologies in these systems, industrial assets are becoming more connected and vulnerable to cyber attacks.
According to a report by the SANS Institute, 71% of industrial organizations have experienced a cyber attack on their industrial control systems
Cybersecurity in connected industrial asset management refers to the implementation of security measures to protect industrial assets from unauthorized access, control, and disruption. IIoT assets, such as ICS, PLC, and SCADA, are particularly at risk because they control critical infrastructure and industrial processes.
How are today’s Industrial Organizations Stacking up in Cybersecurity?
The level of cybersecurity in industrial organizations varies widely. Some organizations have implemented robust security measures to protect their industrial control systems (ICS) and operational technology (OT), while others have not yet fully addressed the cyber risks to their systems.
According to a report by Cybersecurity Ventures, the global cost of cybercrime is expected to reach $10.5 trillion annually by 2025. This includes costs associated with damage to industrial control systems and other operational technology.
The global market for industrial cybersecurity is also expected to grow from $4.9 billion in 2020 to $13.5 billion by 2025, at a CAGR of 22.4%, according to a report by Cybersecurity Ventures.
These statistics indicate that industrial organizations are facing growing threats from cyber attacks and the cost of these attacks is also increasing. As a result, industrial organizations need to take proactive steps to protect their industrial control systems and operational technology from cyber threats.
Bottlenecks that are Preventing in Advancement of Industrial Cybersecurity
Industrial organizations have generally been slower to adopt cybersecurity measures than other industries, but this is starting to change. However, many industrial organisations still struggle with implementing effective cybersecurity measures, due to a variety of factors:
- Legacy systems: Many industries still rely on legacy systems that were not designed with cybersecurity in mind, making them more vulnerable to attacks.
- Limited budgets: Cybersecurity can be costly, and many industrial organizations may have limited budgets for cybersecurity measures.
- Lack of expertise: Industrial organizations may not have the in-house expertise to understand and address cybersecurity risks.
- Complex networks: Industrial control systems are often complex and interconnected, making it difficult to secure them effectively.
- Lack of visibility: Many industrial organizations lack visibility into their networks and systems, making it difficult to identify and respond to cyber threats.
However, the risks are still high in the industry and cyber attacks targeting industrial control systems are increasing in frequency, and the impact of a successful attack on industrial organizations can be severe. It is important for industrial organizations to continue to monitor and adapt their cybersecurity measures to stay ahead of emerging threats.
What are the Main Challenges when Securing IoT Devices?
The main challenges when securing OT and IoT networks are related to industry 4.0, asset management and vulnerability. As more devices are connected to the network, more cyberattacks become possible. Companies must ensure that their OT and IoT networks are secure to protect their assets.
Some of the main challenges when securing industrial IoT devices include:
1. Lack of security by design: Many IoT devices were not designed with security in mind, making them vulnerable to attacks.
2. Limited resources: IoT devices often have limited computing power, memory, and storage, which can make it difficult to run security software.
3. Complex and diverse ecosystem: IoT devices are often part of a larger ecosystem, and securing them can be challenging due to the diversity of devices, protocols, and vendors.
4. Inadequate software updates: IoT devices may not receive regular software updates to fix security vulnerabilities, leaving them exposed to attacks.
5. Inadequate network security: IoT devices are often connected to networks that may not be properly secured, allowing attackers to access the devices.
6. Lack of standardization: There is a lack of standardization in the IoT industry, making it difficult to develop a one-size-fits-all approach to security.
7. Difficulty in identifying and responding to threats: It can be difficult to identify and respond to threats on IoT devices, as many devices lack the capability to generate detailed logs or alerts.
Importance of Building Cybersecurity into IoT Devices
The internet of things (IoT) is revolutionizing the way we interact with connected devices. As these devices are increasingly collecting and sharing data, it is becoming more important to priorities cybersecurity when building them. Cybersecurity is the practice of protecting our data and information from unauthorized access or manipulation.
IoT asset management involves developing security protocols for each device in order to protect industry assets and manufacturers from malicious actors. While this process can be complex, investing in secure protocols now will help prevent security breaches from occurring in the future.
Additionally, strengthening cybersecurity measures can provide a competitive edge over other companies who may not have invested as heavily in their security infrastructure. In short, establishing secure protocols on IoT devices is essential to ensure that all participants remain safe and secure while taking advantage of the digital world’s benefits.
Cost of Staying still for Industries that Needs Cybersecurity
There are several costs associated with not taking action to improve cybersecurity in industrial organizations. These can include:
Financial Losses
Industrial control systems (ICS) and other operational technology (OT) are critical to the operation of manufacturing, energy, and other critical infrastructure industries. If these systems are compromised by a cyber attack, it can result in production downtime, damage to equipment, and financial losses.
Reputation Damage
A cyber attack on an industrial organization can also result in significant damage to the organization’s reputation. This can make it difficult to attract new customers and retain existing ones, leading to further financial losses.
Legal and Compliance Costs
Many industries are subject to regulations and standards that require organizations to implement certain cybersecurity measures. Failure to comply with these regulations can result in significant fines and penalties.
Physical Damage
Some cyber attacks on industrial control systems can also result in physical damage. For example, a cyber attack on a power grid could cause a power outage, leading to physical damage to equipment and potential harm to people.
Loss of Intellectual Property
failure to protect industrial control systems and operational technology from cyber attacks can lead to loss of intellectual property and trade secrets, which can have a long-term negative impact on the organization.
Loss of Competitive Edge
As more and more organizations are investing in cybersecurity, those who don’t invest in cybersecurity will fall behind in terms of competitiveness.
Cost of not taking action to improve cybersecurity in industrial organizations can be significant and can result in financial losses, reputation damage, legal and compliance costs, physical damage, loss of intellectual property and loss of competitive edge.
How do Industrial Asset Manufacturers Make Sure of Industrial Cyber Security?
Industrial asset manufacturers can ensure industrial cyber security by implementing a combination of technical and organisational measures. Some common measures include:
1. Network segmentation: separating control systems from business networks to limit the potential damage of a cyber attack.
2. Firewalls and intrusion detection systems: placing these security measures at key points in the network to monitor for and block malicious traffic.
3. Security patches and software updates: regularly updating software and firmware to address known vulnerabilities.
4. Cybersecurity training: providing regular training for employees to help them understand the risks and how to mitigate them.
5. Vendor management: carefully managing relationships with vendors and third-party service providers to ensure they follow appropriate security protocols.
6. Regular security assessments and penetration testing: regularly testing the system to identify and address any vulnerabilities.
7. Implementing an incident response plan: Having a plan in place to respond to security incidents and minimise damage.
8. Compliance with industry standards: Adhering to relevant regulations and standards for industrial cyber security, such as ISA/IEC 62443, NIST 800-82, and NIST SP 800-53.
How Kemsys can Help?
Kemsys follows Microsoft’s Seven Properties of Highly Secure Devices as a set of guidelines to outline the key characteristics that a device must possess in order to be considered highly secure. These properties are designed to help organizations assess the security of their devices and identify areas where improvements can be made.
The seven properties include:
- Hardware-based root of trust
- Small trusted computing base
- Defense in depth
- Compartmentalization
- Certificate-based authentication
- Renewable security
- Failure Reporting
Each of these properties plays an important role in ensuring that a device is protected against a wide range of threats, including malware, hacking, and other forms of cyber attack.
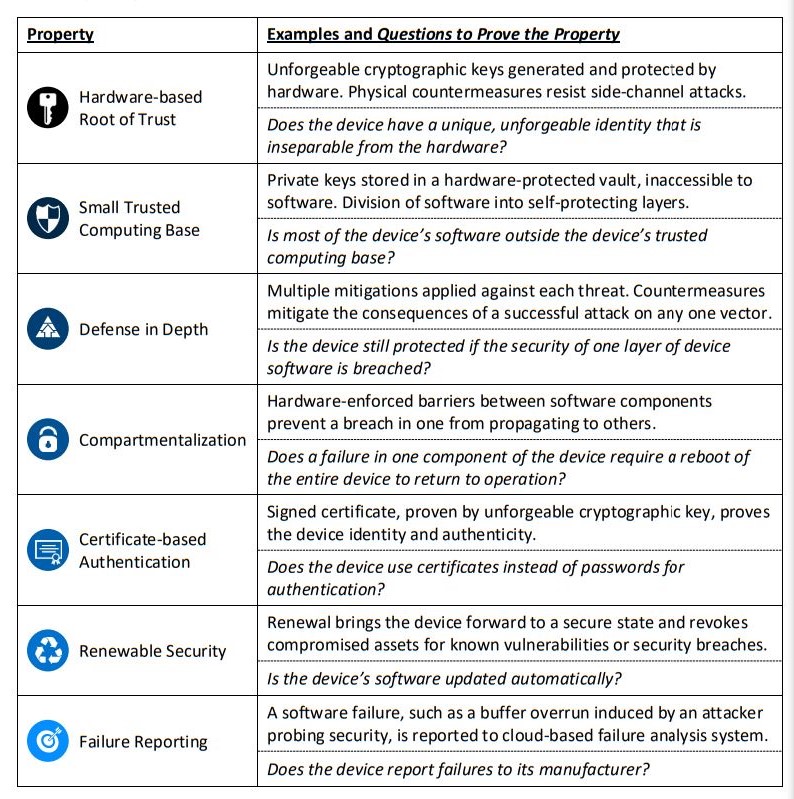
Kemsys follows these properties to help industrial organizations significantly reduce their risk of data breaches and other security incidents.
Conclusion
In conclusion, cybersecurity in industrial asset management is a critical issue that requires the attention of industrial organizations. With the increasing connectivity of industrial systems and the growing number of IoT devices, the risk of cyber attacks on industrial assets is significant.
Industrial organizations must take proactive measures to protect their systems, including implementing technical and organizational measures, such as firewalls and intrusion detection systems, regular software updates and patches, incident response plans and employee training programs.